NASA admits it has under-calculated risk from meteors, etc., some claim comet ISON is the destructive ‘planet Nibiru,’ but what does the Bible teach?
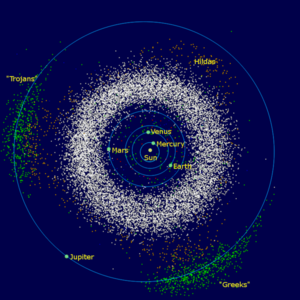
The asteroid belt (shown in white) is located between the orbits of Mars and Jupiter.
NASA has revealed that its latest research shows that it has underestimated the risk of significant objects from outer space impacting the Earth:
New, DEVASTATING Chelyabinsk METEOR STRIKE: ‘7x as likely’ as thought
NASA has revealed new research on the Chelyabinsk meteorite that exploded over Russia in February, and the findings aren’t good: not only does it look like the astronomic models about the number of similar-sized things reaching Earth are wrong, but also the damage they can do is much greater than expected.
“If you look at the number of impacts detected by US government sensors over the past few decades you find the impact rate of kiloton-class objects is greater than would be indicated by the telescopic surveys,” said Bill Cooke, meteoroid environment office lead at NASA’s Marshall Space Flight Center at a press conference on Wednesday.
“Over the past few decades we’ve seen an impact rate about seven times greater than the current state of the telescopic surveys would indicate.”
Cooke said that as the current state of asteroid surveys was expanded he expected we would find more meteorites…the amount of heat they generate, and the damage caused by the shockwave of air they push before them as they come down through the atmosphere, was significantly underestimated. http://www.theregister.co.uk/2013/11/06/chelyabinsksized_meteors_impacts_seven_times_more_common_than_first_thought/
So, the risk is bigger than NASA has tended to think. For more information on the Chelyabinsk meteorite, check out the post Meteor explosion in Russia not the end of the world, but is a sign.
Here is some additional information about asteroids and the asteroid belt:
Most asteroids lie in a vast ring between the orbits of Mars and Jupiter. This main belt holds more than 200 asteroids larger than 60 miles (100 kilometers) in diameter. Scientists estimate the asteroid belt also contains more than 750,000 asteroids larger than three-fifths of a mile (1 kilometer) in diameter and millions of smaller ones. Not everything in the main belt is an asteroid — for instance, comets have recently been discovered there, and Ceres, once thought of only as an asteroid, is now also considered a dwarf planet.
Many asteroids lie outside the main belt. For instance, a number of asteroids called Trojans lie along Jupiter’s orbital path…An asteroid capable of global disaster would have to be more than a quarter-mile wide. Researchers have estimated that such an impact would raise enough dust into the atmosphere to effectively create a “nuclear winter,” severely disrupting agriculture around the world. Asteroids that large strike Earth only once every 1,000 centuries on average, NASA officials say. http://www.space.com/51-asteroids-formation-discovery-and-exploration.html
About 1,000 asteroids big enough to cause catastrophic damage if they hit Earth are orbiting relatively nearby, a NASA survey shows…An asteroid or comet between 5 and 10 km (3.1 and 6.2 miles) in diameter is believed to have smashed into Earth some 65 million years ago, triggering global climate changes that led to the extinction of dinosaurs and other animals. “We know something that big could wipe out mostly all life on Earth,” Mainzer said. http://www.reuters.com/article/2011/12/07/us-space-asteroids-idUSTRE7B615O20111207
Speaking of objects from space, a major comet is expected to be visible soon:
November 7, 2013
A potentially bright comet will be visible in November and December…
Comet ISON (C/2012) will swing close to the sun at the end of this month and should be visible in the pre-dawn sky in December. This comet is predicted to be dramatic, but comets are unpredictable.
David Levy, author and comet discoverer, says, “Comets are like cats; they have tails and do whatever they want.” http://azstarnet.com/lifestyles/column/sky-spy-dramatic-comet-ison-should-be-visible/article_82945bdc-92fa-59f0-b270-05f056822530.html
Is it dangerous? Comet ISON presents no danger at all to life on Earth. Absolutely none. There is not even the most minute chance that it could collide with our planet (anyone who says otherwise is completely misinformed- note I have toned my language here down after some justified criticism). It will pass about 0.42 AU (63 million km) from Earth on 26 December 2013. I cannot believe anyone thinks this is a near miss. Earth may pass through the comet’s debris trail on 16 January 2014 and we may just be lucky to observe a meteor shower that night . http://www.armaghplanet.com/blog/ison-things-you-need-to-know.html
Now, I have known for quite sometime that a few have claimed that comet ISON is dangerous and can lead to the end of the world in 2013 or 2014. Here are a couple of reports on that:
When is a comet not just a comet, but a divine warning sign like Jesus spoke of coming in the end times? If you do not know how to answer that, Comet “ISON” may test you with fear and
anxiety in 2013. Doomsday watchers are already predicting that Comet ISON is Planet X, Nibiru, Wormwood, or a gravitational earthquake/deep impact threat. Alternatively, some predict it will make a spectacular daytime visible sign in the sky one month before Christ’s return (yes, on Christmas, 2013). http://www.escapeallthesethings.com/comet-ison-nibiru.htm
According to this just released video from CourageousNerd z, the approaching Comet ISON IS Nibiru! The videographer also goes on to claim that human life will not exist after January of 2014 and that NASA knows it and is lying to all of us and knows that the ‘end is near’. http://vaticproject.blogspot.com/2013/08/it-turns-out-comet-ison-is-nibiru-thats.html
The truth is that it is NOT possible for Jesus to return next month or for the world to end in 2013 or 2014.
Yet, it is true that something from space, probably an asteroid or a comet, is prophesied in the Bible to hit the Earth and cause massive damage.
Over 1900 years ago, the Apostle John was inspired to write the following in the Book of Revelation 8:10-11:
Then the third angel sounded: And a great star fell from heaven, burning like a torch, and it fell on a third of the rivers and on the springs of water. The name of the star is Wormwood. A third of the waters became wormwood, and many men died from the water, because it was made bitter.
A large comet hitting the earth would also seem to have similar effects to that of a medium-sized asteroid. And having something actually hit the earth and do massive damage is predicted in the Bible.
But it cannot hit next month.
Why?
If you look at the sequence of events that proceed Wormwood, it is obvious that all cannot happen between now and next month. Notice that the first nine verses happen prior to Wormwood falling from heaven:
1 When He opened the seventh seal, there was silence in heaven for about half an hour. 2 And I saw the seven angels who stand before God, and to them were given seven trumpets. 3 Then another angel, having a golden censer, came and stood at the altar. He was given much incense, that he should offer it with the prayers of all the saints upon the golden altar which was before the throne. 4 And the smoke of the incense, with the prayers of the saints, ascended before God from the angel’s hand. 5 Then the angel took the censer, filled it with fire from the altar, and threw it to the earth. And there were noises, thunderings, lightnings, and an earthquake.
6 So the seven angels who had the seven trumpets prepared themselves to sound.
7 The first angel sounded: And hail and fire followed, mingled with blood, and they were thrown to the earth. And a third of the trees were burned up, and all green grass was burned up.
8 Then the second angel sounded: And something like a great mountain burning with fire was thrown into the sea, and a third of the sea became blood. 9 And a third of the living creatures in the sea died, and a third of the ships were destroyed.
10 Then the third angel sounded: And a great star fell from heaven, burning like a torch, and it fell on a third of the rivers and on the springs of water. 11 The name of the star is Wormwood. A third of the waters became wormwood, and many men died from the water, because it was made bitter. (Revelation 8:1-11)
It should also be noted that there are MANY EVENTS that also have to take place before the above events as well. Notice that Wormwood does not fall until after the third trumpet associated with the seventh seal of Revelation is blown. Well, this would mean that the fifth and sixth seal would also have already been opened–which are mentioned in Revelation 6:7-17, and the 144,000 numbered as shown in Revelation 7. And I should add that the fifth seal of Revelation cannot possibly be opened for at least 3 1/2 years from now (see When Will the Great Tribulation Begin? 2013, 2014, or 2015?), with over 4 years the likely minimum.
Because of all of that, Jesus cannot possibly return before 2021. In December of 2012, I made a post titled Ten ‘End of the World Predictions’ That Will Be Proven False This Month. Of course, I was right about that, and one of the ten had to do with allegedly ‘Planet Nibiru’ hitting the Earth in December 2012. Planet Nibiru per se does not exist, but Wormwood does–but again Wormwood cannot hit for several years at the earliest. That does not mean that there cannot be any problems from meteorites, comets, asteroids, solar flares, etc. But it does mean that the world will not end for at least several years.
I should also mention that certain Protestant pastors have suggested that the appearance of ‘blood moons’ in 2014 and 2015 could be a sign that:
- The Great Tribulation may begin
- The Day of the Lord may start
- Jesus may return
None of which will happen in 2014 or 2015 as there are too many biblically-required events that have to happen first.
We in the Continuing Church of God “have also a more sure word of prophecy; whereunto ye do well that ye take heed, as unto a light that shineth in a dark place” (2 Peter 1:19, KJV).
And we have the sure word because we believe what the Bible teaches and not opinions of humans that do not agree with the Bible.
Some items of possibly related interest may include:
Wormwood and Planet Nibiru Is Comet ISON really Planet X? Will the Earth be devastated by this in 2014?
Bible: Superstition or Authority? Should you rely on the Bible? Is it reliable? Herbert W. Armstrong wrote this as a booklet on this important subject.
Does God Have a 6,000 Year Plan? What Year Does the 6,000 Years End? Was a 6000 year time allowed for humans to rule followed by a literal thousand year reign of Christ on Earth taught by the early Christians? Does God have 7,000 year plan? What year may the six thousand years of human rule end? When will Jesus return? 2021 or 20xx? There is also a video titled The 6000 Year Plan: Is the end of humanity’s reign almost up?
When Will the Great Tribulation Begin? 2013, 2014, or 2015? Can the Great Tribulation begin today? What happens before the Great Tribulation in the “beginning of sorrows”? What happens in the Great Tribulation and the Day of the Lord? Is this the time of the Gentiles? When is the earliest that the Great Tribulation can begin? What is the Day of the Lord? Who are the 144,000? Here is a version of the article in the Spanish language: ¿Puede comenzar la Gran Tribulación en 2013 o 2014? ¿Es el Tiempo de los Gentiles? You can also see the English language video The Great Tribulation Will Not Begin Before 2017.
Blood Moons and Prophecy There are four ‘blood moons’ expected in 2014 and 2015. Do they signal the Day of the Lord or the return of Jesus Christ? A related YouTube video is also available: Blood Moons, Prophecy, 2014, and 2015.
 |
Tweet |
|